Table of Contents
- Report Overview
- Top Market Takeaways
- Key Insights Summary
- How Zero Trust Network Access is Reshaping the Future?
- Scope and Research Methodology
- Key Forces Driving Market Expansion
- Emerging Trends Analysis
- Driver Analysis
- Restraint Analysis
- Opportunity Analysis
- Challenge Analysis
- Competitive Analysis
- Key Market Segments
- Top Key Players in the Market
- Conclusion
- Report Scope
Report Overview
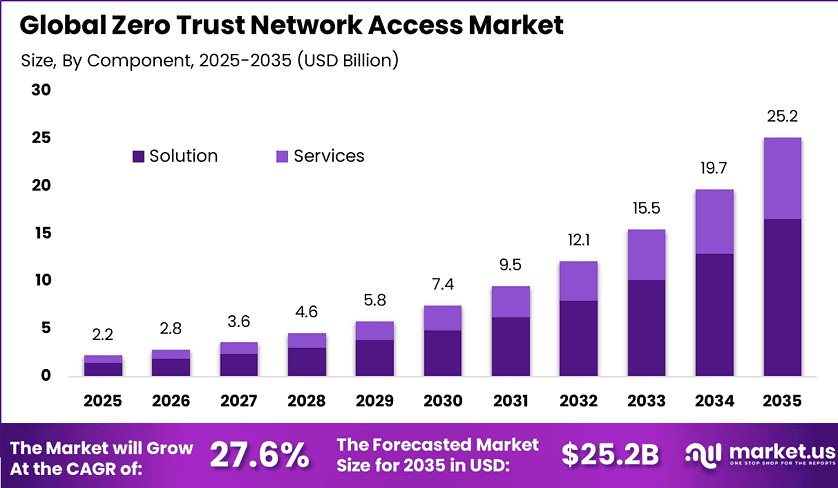
The global Zero Trust Network Access market is projected to reach approximately USD 25.2 billion by 2035, rising from USD 2.2 billion in 2025, reflecting a strong compound annual growth rate of 27.6% during the forecast period. This growth is being driven by the rising frequency of cyber threats, increasing adoption of remote work models, and the need for advanced identity-based security frameworks. In 2025, North America held a dominant position with more than 35.3% share, supported by strong enterprise adoption and regulatory alignment.
Organizations are increasingly shifting away from traditional perimeter-based security models toward zero trust architectures that continuously verify users and devices. This approach reduces the risk of unauthorized access and enhances network visibility. The growing complexity of IT environments and cloud adoption is further accelerating the need for ZTNA solutions. As cybersecurity becomes a strategic priority, the market is expected to expand significantly.
Top Market Takeaways
- The market is expected to grow from USD 2.2 billion in 2025 to USD 25.2 billion by 2035, reflecting a 27.6% CAGR.
- The solution segment dominated with 65.7% share, driven by demand for integrated security platforms.
- On-premise deployment led with 60.3% share, supported by control and data security requirements.
- Large enterprises held 70.5% share, reflecting higher investment in cybersecurity infrastructure.
- Remote access security accounted for 37.8% of demand, driven by hybrid work environments.
- BFSI emerged as the leading end-use sector with 38.8% share due to high security requirements.
- North America held 35.3% share, while the U.S. market reached USD 0.68 billion with strong growth.
Key Insights Summary
- Full implementation of ZTNA can prevent up to 78% of potential security breaches.
- Around 87% of organizations report a decline in security incidents after adoption.
- ZTNA reduces phishing attacks by 47%, ransomware incidents by 62%, and insider threats by 55%.
- Threat detection and response times improve by up to 50%.
- Approximately 52% of organizations have fully deployed ZTNA, while 38% are in partial implementation stages.
- About 35% of enterprises identify legacy infrastructure complexity as a major barrier.
- Nearly 54% of IT leaders cite budget constraints, and 35% report lack of expertise as challenges.
- Around 68% of enterprises are replacing or supplementing traditional VPNs with ZTNA solutions.
- By 2025, nearly 95% of U.S. federal agencies are expected to align with zero trust compliance mandates.
How Zero Trust Network Access is Reshaping the Future?
Zero Trust Network Access is transforming cybersecurity by eliminating implicit trust within networks and enforcing strict identity verification for every access request. This approach ensures that users and devices are continuously authenticated and authorized based on context and behavior. It significantly reduces the attack surface and limits lateral movement within networks. As a result, organizations can better protect sensitive data and critical systems.
ZTNA is also enabling secure and flexible remote work environments by providing controlled access to applications without exposing the entire network. Employees can securely connect from different locations while maintaining strong security standards. This improves productivity while minimizing risks associated with remote access. Over time, ZTNA is becoming a foundational element of modern digital security strategies.
Scope and Research Methodology
The scope of the ZTNA market includes solutions that provide secure, identity-based access to applications and systems across cloud and on-premise environments. It covers components such as authentication systems, access management platforms, and network security tools. The analysis includes adoption across industries such as BFSI, healthcare, IT, and government. Both cloud-based and on-premise deployments are considered within the scope.
The research methodology is based on evaluating cybersecurity trends, enterprise adoption patterns, and evolving regulatory requirements. Publicly available information and observed implementation practices have been analyzed to ensure accuracy. Validation is supported by security incident trends and technological advancements. A structured and consistent framework ensures reliability and credibility of insights.
Key Forces Driving Market Expansion
One of the primary forces driving market growth is the increasing sophistication of cyber threats, including ransomware, phishing, and insider attacks. Organizations are seeking advanced security frameworks that provide continuous monitoring and verification. ZTNA helps reduce vulnerabilities and improve threat detection capabilities. This is encouraging widespread adoption across industries.
Another key force is the growing adoption of hybrid and remote work environments. Employees require secure access to enterprise applications from various locations and devices. ZTNA provides secure connectivity without relying on traditional VPNs, which often have limitations. This shift in work models is significantly contributing to market expansion.
Emerging Trends Analysis
A major trend in the market is the integration of ZTNA with cloud security platforms and identity management systems. Organizations are adopting unified security solutions to improve visibility and control across distributed environments. This trend is supporting scalability and flexibility in security operations. It is gaining traction as cloud adoption continues to rise.
Another emerging trend is the use of artificial intelligence and analytics within ZTNA solutions. These technologies enable real-time threat detection, anomaly identification, and automated response mechanisms. This enhances the overall effectiveness of security frameworks. The trend is expanding as organizations seek more proactive security approaches.
Driver Analysis
A key driver is the strong adoption of ZTNA solutions among large enterprises, which accounted for a dominant share of the market. These organizations require robust security frameworks to protect complex IT infrastructures. ZTNA provides comprehensive access control and monitoring capabilities. This is driving market growth.
Another driver is the increasing demand for remote access security, which has emerged as a leading application area. ZTNA ensures secure access for distributed workforces without compromising network integrity. This improves both security and operational efficiency. The growing reliance on remote work is encouraging adoption.
Restraint Analysis
One of the major restraints is the complexity associated with integrating ZTNA solutions into existing legacy infrastructure. Many organizations operate outdated systems that are not compatible with modern security frameworks. This increases implementation time and cost. It can slow adoption, especially in traditional industries.
Another restraint is budget limitations and lack of in-house expertise. Many organizations face challenges in allocating resources for advanced cybersecurity solutions. Additionally, the shortage of skilled professionals makes deployment and management more difficult. These factors can hinder market growth.
Opportunity Analysis
A significant opportunity lies in the replacement of traditional VPN solutions with ZTNA frameworks. Organizations are increasingly recognizing the limitations of VPNs in modern environments. ZTNA offers more secure and scalable alternatives for access management. This is creating strong growth potential for the market.
Another opportunity is the increasing adoption of zero trust frameworks in government and regulated sectors. Compliance requirements are driving the need for advanced security solutions. ZTNA helps organizations meet these requirements effectively. This is expanding its application across multiple sectors.
Challenge Analysis
A key challenge is managing the complexity of implementing a zero trust architecture. Organizations must redesign their security frameworks and processes to align with zero trust principles. This requires significant planning and coordination. It can delay deployment and increase operational challenges.
Another challenge is balancing security with user experience. Strict access controls can sometimes create friction for users if not implemented properly. Organizations must ensure seamless access while maintaining high security standards. Achieving this balance is critical for successful adoption.
Competitive Analysis
The competitive landscape is characterized by increasing investment in advanced cybersecurity solutions and identity-based access technologies. Companies are focusing on developing integrated platforms that combine access control, monitoring, and analytics. Innovation in security architecture and user experience is a key differentiator. This is intensifying competition in the market.
In addition, organizations are engaging in partnerships and collaborations to enhance their capabilities and expand market reach. The focus is on delivering scalable and secure solutions that meet evolving enterprise needs. Competitive strategies also include improving interoperability with existing systems. This is shaping a dynamic and evolving market environment.
Key Market Segments
By Component
- Solution
- Services
By Deployment
- Cloud
- On-Premise
- Hybrid
By Enterprise Size
- Small & Medium Enterprises
- Large Enterprises
By Application
- Remote Access Security
- Application Access Control
- Secure Cloud Connectivity
- Network Monitoring & Compliance
- Others
By End Use
- BFSI
- IT and Telecommunications
- Healthcare
- Government & Defense
- Retail & E-Commerce
- Energy & Utilities
- Education
- Others
Top Key Players in the Market
- Akamai Technologies
- AppGate
- Check Point Software Technologies Ltd.
- Cisco Systems, Inc.
- Cloudflare, Inc.
- Fortinet, Inc.
- Menlo Security
- Netskope
- Nord Security
- Okta
- Omega Systems
- Palo Alto Networks
- Twingate
- Zero Networks
- Zscaler, Inc.
- Others
Conclusion
The Zero Trust Network Access market is experiencing rapid growth, driven by the increasing need for advanced cybersecurity, secure remote access, and regulatory compliance. Organizations are adopting ZTNA to enhance security, reduce risks, and improve visibility across networks. The transition from traditional security models to zero trust frameworks is transforming cybersecurity practices.
Despite challenges related to cost, integration, and complexity, the overall outlook remains positive. Continued advancements in security technologies and increasing adoption across industries are expected to support long-term growth. As digital transformation accelerates, ZTNA will play a central role in securing modern enterprise environments. The market is positioned for sustained expansion with significant impact on global cybersecurity systems.
Report Scope
| Report Features | Description |
|---|---|
| Market Value (2025) | USD 2.2 Bn |
| Forecast Revenue (2035) | USD 25.2 Bn |
| CAGR (2026-2035) | 27.6% |
| Base Year for Estimation | 2025 |
| Historic Period | 2020-2024 |
| Forecast Period | 2026-2035 |
| Report Coverage | Revenue forecast, AI impact on Market trends, Share Insights, Company ranking, competitive landscape, Recent Developments, Market Dynamics and Emerging Trends |
| Segments Covered | By Component (Solution, Services), By Deployment (Cloud, On-Premise, Hybrid), By Enterprise Size (Small & Medium Enterprises, Large Enterprises), By Application (Remote Access Security, Application Access Control, Secure Cloud Connectivity, Network Monitoring & Compliance, Others), By End Use (BFSI, IT and Telecommunications, Healthcare, Government & Defense, Retail & E-Commerce, Energy & Utilities, Education, Others) |
| Regional Analysis | North America – US, Canada; Europe – Germany, France, The UK, Spain, Italy, Russia, Netherlands, Rest of Europe; Asia Pacific – China, Japan, South Korea, India, New Zealand, Singapore, Thailand, Vietnam, Rest of Latin America; Latin America – Brazil, Mexico, Rest of Latin America; Middle East & Africa – South Africa, Saudi Arabia, UAE, Rest of MEA |
Discuss your needs with our analyst
Please share your requirements with more details so our analyst can check if they can solve your problem(s)



